PARTY as the keyword:
MAKE SURE JOE IS GONE BY SEVEN. ALICE.Now, we create our ciphertext alphabet and compare to our plaintext alphabet
plaintext: A B C D E F G H I J K L M N O P Q R S T U V W X Y Z ciphertext: P A R T Y B C D E F G H I J K L M N O Q S U V W X ZSo our encrypted message reads:
IPGY OSNY FKY EO CKJY AX OYWYJ. PHERY.To decrypt this message, Bob needs to know that the keyword is party. Once he knows that, he swaps the position of the alphabets:
ciphertext: P A R T Y B C D E F G H I J K L M N O Q S U V W X Z plaintext: A B C D E F G H I J K L M N O P Q R S T U V W X Y Zand reads the message.
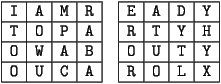
I AM READY TO PARTY! HOW ABOUT YOU? CAROL.Notice that without punctuation, there are 31 characters in Carol's message. Adding a dummy
X at the end makes 32. Now draw two
four by four square, and write the message out, one letter in each box
going all the way across both boxes, one row at a time:
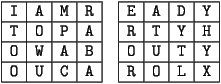
Now, to get her encrypted message, Carol writes the last column, top to bottom. Then she writes the second to last column, and so forth. Her encrypted message looks like:
YHYX DYTL ATUO EROR RABA MPAC AOWU ITOOAlice could have arranged the columns in any order she wanted to. Of course, to decrypt the message, Bob needs to know both what size square Alice used and what order in which she wrote the columns.
PARTY TIME!!!First, she writes the numerical date (8/30/2008) over her message, repeating as often as necessary:
83020 0883020 PARTY TIME!!!Next, she shifts each character to a number and then adds to that the number written directly above, reducing each modulo 41 gives the ciphertext:
2404182225 20172108384038So long as the recipients know the date that was used to encrypt the message, it is as easy to decrypt as the shift cipher!
Now write a short reply message and encode it using the date cipher. Trade and decrypt.